课程描述
Ethical Hacking / Penetration Testing & bug Bounty Hunting is a comprehensive training of all kinds of ethical hacking methods . Ethical hacking is a kind of authorized hacking that is used to detect weaknesses, threats and potential security breaches . This course is intended for training this type of hack, along with penetration testing and award-winning bug hunting systems . This course is fully functional and goes live testing on real sites . During this tutorial, you will learn a variety of vulnerability points . The training begins with the foundations and the definition of a vulnerability, and then the attack teaches them with the help of several passing techniques . In addition to using these vulnerabilities, you will learn how to repair and fix them .
Ethical Hacking / Penetration Testing & bug Bounty Hunting是对各种道德黑客方法的综合培训。道德黑客攻击是一种经过授权的黑客攻击,用于检测弱点、威胁和潜在的安全漏洞。本课程旨在培训此类黑客,以及渗透测试和屡获殊荣的漏洞搜索系统。本课程功能齐全,并在真实站点上进行实时测试。在本教程中,您将学习各种漏洞点。培训从基础知识和漏洞定义开始,然后在几种传递技术的帮助下进行攻击。除了使用这些漏洞之外,您还将学习如何修复和修复它们。
With this tutorial, you can work professionally on many bug hunting platforms such as Bugcrowd, HackerOne and Open Bug Bounty . This tutorial starts from OWASP (a project in the field of online security ) and goes on to how to gain access to user accounts . As examples, live, during this training, vulnerability, website, government of India ( NCIIPC ), and several company is to expose vulnerabilities of your declaration of readiness were discovered and reported to you . Scripting XSS, etc., pass from authentication multi-step attack using the lack of restrictions of the application. attack CSRF and CORS, including the topics covered by this training are .
通过本教程,您可以专业地在许多漏洞搜寻平台上工作,例如 Bugcrowd、HackerOne 和 Open Bug Bounty。本教程从 OWASP(在线安全领域的一个项目)开始,然后介绍如何获得对用户帐户的访问权限。例如,在本次培训期间,漏洞、网站、印度政府 (NCIIPC) 和几家公司将揭露您准备就绪声明的漏洞,并已发现并报告给您。脚本 XSS 等,通过使用缺乏应用程序限制的身份验证多步攻击。攻击 CSRF 和 CORS,包括本次培训涵盖的主题是 .
What things to learn; 学什么东西
OWASP 10 basic concepts compare versions and variations
Bonus bug hunting live tips and tricks
Recognizing and decomposing HackerOne reports
Bugging requests to bourpsuit proxy assistance and gaining full access to the target server
Passing a variety of two-stage verification methods and not verifying the robot
Discover various vulnerabilities, access to user accounts
Understanding how to enter different award-winning bug discovery platforms : Hackerone, OpenBugBounty, Bugcrowd
And …
OWASP 10 基本概念 比较版本和变体 奖金 bug hunting live 提示和技巧 识别和分解 HackerOne 报告 窃听请求 bourpsuit 代理协助并获得对目标服务器的完全访问权限 通过各种两阶段验证方法而不验证机器人 发现各种漏洞,访问用户帐户 了解如何进入不同的获奖漏洞发现平台:Hackerone、OpenBugBounty、Bugcrowd 和……
This training suits people who; 本次培训适合以下人群
Anyone interested in hacking and testing intrusion to websites and web apps
People who tend to work in the field of penetration testing and prized bug hunting or training them to others
People who are on the ground of cybersecurity are beginners and want to be on the analytical side and even professional people
Developers who want to discover and fix the vulnerabilities of their applications
任何对黑客攻击和测试网站和网络应用程序入侵感兴趣的人 倾向于在渗透测试和珍贵的漏洞搜索领域工作或向他人培训他们的人 从事网络安全工作的人是初学者,希望处于分析方面甚至专业人士 想要发现并修复其应用程序漏洞的开发人员
Specifications of Ethical Hacking / Penetration Testing & bug Bounty Hunting; 道德黑客/渗透测试和漏洞赏金猎人的规范
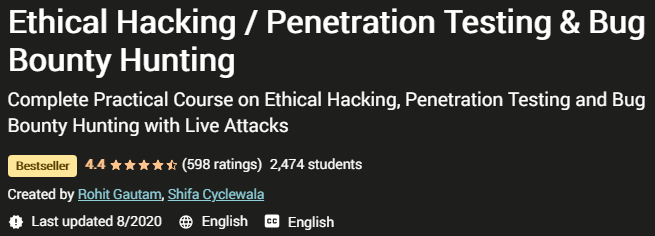
Publisher: Udemy
Lecturer: Rohit Gautam, Shifa Cyclewala
Language: English
Training level: from preliminary to advanced
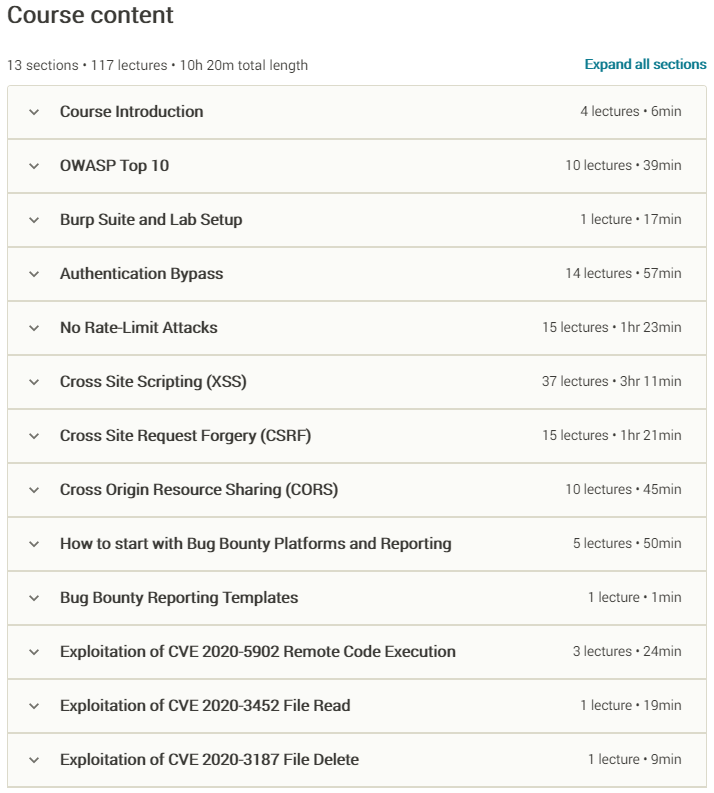
Number of lessons: 117 lessons in 13 sections
Duration: 10h 20m
出版商:Udemy 讲师:Rohit Gautam, Shifa Cyclewala 语言:英语 培训水平:从初级到高级 课时数:13 节 117 课时长:10 小时 20 米
Head seasons; 头四季
Prerequisites; 先决条件
- Basic IT Skills
- 基本信息技术技能
- No Linux, programming or hacking knowledge required.
- 无需 Linux、编程或黑客知识。
- Computer with a minimum of 4GB ram/memory & Internet Connection
- 具有至少 4GB 内存/内存和互联网连接的计算机
- Operating System: Windows / OS X / Linux
- 操作系统:Windows / OS X / Linux
Images; 图片
Sample movie; 样片
Installation guide; 安装指南
After the Extract with the Player your custom view.
在使用播放器提取您的自定义视图之后。
Subtitles: English
字幕:英文
Quality: 720p
画质:720p